❑This chapter (and related linked chapters) provides a sample of, and links to, many of the Definitions, how-to information for Installation and Data Entry Requirements, and instructions for the specific Processes and Procedures required by the Third Edition UL® 1981 Standard of the Classified MKMSCS (and MKMS) application, and its associated third party hardware and software. This chapter includes:
1.Portions of Section 5(1-64) Glossary of the Third Edition UL® 1981 Standard;
2.Special information provided below (and more in the UL Settings, Signal Processing & Reporting Procedures chapter) for compliance with the 6 - Automation Access Security and 7 - Automation Multiplicity items in the Third Edition UL® 1981 Standard Section.
3.Additional information associated with compliance with Sections 8 to 13 of the Third Edition UL® 1981 Standard.
4.A list of Central Station Reports
5.Other Third Edition UL® 1981 Standard Setup Considerations:
a.Auditing - Auditing of the additions, modifications and deletions made in all Forms is mandatory.
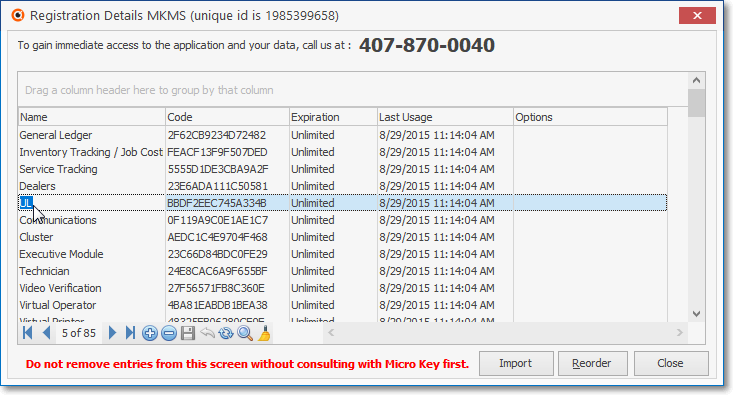
Registration Details Form - UL registration entry
▪Users are not allowed to turn off auditing when the UL® 1981 Version is Registered (i.e., Active).
oIn the Employee Groups and User Access Rights Forms. when UL is active, the Audit option box will always be Checked on all Forms.
oNo User will be able to remove that Check Mark.
➢Note: It is important to remember that when an Employee has specific rights assigned by using the User Access Rights Form, those rights granted or restricted by using the User Access Rights Form will override those granted or restricted on the Employee Groups Form! Make sure when restricting or granting any rights or access to a Form or a Field, that those restricted or granted rights are not negated in the User Access Rights Form
b.Priority Levels - Mandatory Priority Levels for specified Alarm Conditions are predefined and may not be changed.
▪The Condition Codes List includes a Priority Level field (also see Signal Priority below, and Priority Levels).
c.Resolution Codes must be defined, and subsequently assigned to each Alarm Signal which has been processed to completion.
❑Other Important Notes and Comments:
•Data Entry - The Subscriber Entries, the associated Central Station Data, and each individual Subscriber Panel CSID (Central Station IDentification number), and the Events, CSID Zones, People To Call, Account Testing, and Medical Information for each CSID are explained in their respective chapters.
✓The UL Classification, UL Response Time, Keys Held, and/or Investigator Required information must be entered (as appropriate) on any applicable Subscriber installation as part of their Central Station Data.
•Hot Back-Up - A continuously energized computer system that is a back-up to the primary system computer and disk drive will be used [see (a) UL Installation Requirements, (b) MKS Systems Status, and (c) MKS Cluster].
•Operation - The details of how to Process Alarms including the explanation of the Processing, Action and Data tabs on the Signal Processing Form, as well as the Verification, Dispatch, Notification and Completion procedures which meet the Third Edition UL® 1981 Standard are detailed in these chapters:
a.There are two methodologies available for structuring exactly how each type of Alarm Condition received from a Subscriber should be handled. These are:
i.Operator Guided Responses - This Operator Guided Response methodology, created to Process Alarm Signals, actually "walks" the Operator through each required step, assuring the proper completion of each of these steps, and in the appropriate order, so that each Alarm Signal - regardless of which Operator Guided Response steps are needed - will be handled correctly.
ii.Action Plans - At many Central Stations, including most that are UL® Listed, individual Subscribers and/or specific Alarm Dealers, may require that a different set of processing instructions be followed for certain Signals or types of Accounts. Therefore, Action Plans are provided for those Active Signals needing a Response by an Operator that cannot be precisely documented using the standard Operator Guided Response.
b.The Alarm Signal Processing standard requires that a Minimum of One (1) Central Station Operator or Supervisor (these persons and their position are identified in the Employees Form) shall be logged on at all times; and if the last Operator attempts to exit Alarm Processing they will be prevented from doing so.
▪A Supervisor may override this behavior - after receiving a warning - which should only be done for the purpose of Testing.
c.Generate Email on Account Modification - A special process (Daily Accounts Modified) designed and documented to comply with Section 6.2.3 - Track User Changes in the Third Edition UL® 1981 Standard will be executed everyday at 1:00am
i.This notification consists of an Email to each Subscriber who has had any Account Information modified within any of the following Tables:
g)Events
ii.Whenever a change occurs in one or more of the Tables listed in i., a.-g. above, it is recorded in an AccountsModified table.
iii.When the UL® Version is Active, the "SendEmailWhenSubscriberDataChanges" option in Company Setting is automatically set to True ("T") which will implement the Daily Accounts Modified process that will notify those Subscribers who have had their information modified within MKMS during the previous day - everyday at 1:00am.
a)If "SendEmailWhenSubscriberDataChanges" is set to False ('F'), it will stop the Daily Accounts Modified notification process.
d.Email Modified Subscribers Now - The Email Modified Subscribers Now Form (designed and documented to comply with the Third Edition UL® 1981 Standard) allows an Operator (or any authorized User) to Email a Change Notification to a Subscriber on demand.
e.UL Categories: All statistics shall be broken down by certificate type, such as
i.UL® Central Station fire alarm systems,
ii.UL® Central station burglar alarm systems,
iii.UL® proprietary burglar alarm systems,
iv.UL® national industrial burglar alarm systems,
v.UL® mercantile burglar alarm systems,
vi.UL® residential burglar alarm systems, and account number
f.Signal Priority - Multiple Function systems shall be configured according to the following functions in descending order of priority (Setting Alarm Condition Priority Levels, UL® Alarm Condition - Priority Ranking ):
1)Fire alarm;
2)Emergency call system; (mass notification / E911 / reverse 911 / fire system);
3)Hold-up or panic alarm;
4)Medical including carbon monoxide;
5)Industrial supervision if a danger can result;
6)Burglar alarm (with line security);
7)Burglar alarm (without line security);
ÙÙÙÙÙÙÙÙ
Above the arrows are required (priorities 2,3,4 may share the same priority number)
8)Supervisory signal
9)Trouble signal;
10)Other.
▪Items 2, 3, and 4 are not prohibited from having equal priority.
•For a list of other Installation Requirements see UL Installation Requirements);
❑An Abbreviated Overview of the definitions and instructions in the Third Edition UL® 1981 Standard is outlined below.
a)It is understood within this Electronic Document that all Third Edition UL® 1981 Standards are relevant and must be implemented when appropriate;
b)The summarized list below may have links to related chapters, and/or provide explanatory comments for implementing this automation system (see Glossary 5.5 below).
➢Explanatory Comments are indicated with the Right Arrow and appear after that Standard is described.
Introduction
❑1 Scope - These requirements cover the design, manufacture, implementation, and support of automation system units and accessories intended to be used in central-stations.
❑2 Components - A component of a product covered by this Standard shall comply with the requirements for that component and shall be used in accordance with its rating established for the intended conditions of use, except where that component involves a feature or characteristic not required by this Standard.
❑3 Units of Measure - Values stated without parentheses are the requirement. Values in parentheses are explanatory or approximate information.
❑4 Undated References - Any undated reference to a code or standard appearing in the requirements of this standard shall be interpreted as referring to the latest edition of that code or standard.
❑5 Glossary (a selection of items in Section 5(1-64) Glossary of the Third Edition UL® 1981 Standard)
5.1 - For the purpose of the Third Edition UL® 1981 Standard, the following definitions apply.
5.2 - Active System - A system that sends one or both of the following signals to the central-station on a regular basis:
a)A signal that the system has been disarmed and the protection removed (commonly referred to as "opened"); or
b)A signal that the system has been armed and the protection activated (commonly referred to as "closed")
▪If an alarm system sends opening and closing (disarm and arm) signals, it is considered to be an active system.
▪Supervisory check-in signals transmitted from a system does not make it an active system.
5.3 - Alarm Monitoring Software - The sequence of instructions that tells the hardware how to handle the incoming signals and instructions from the keyboard.
▪The alarm-monitoring software controls how the messages are stored in memory (SPA) and how they are displayed at the operator station and printers (Signal Processing).
5.4 - Alarm Signal
▪A signal from an alarm system which requires immediate action.
▪A signal, such as the alarm initiated from a manual box, a water flow switch, an automatic fire detector, an intrusion detection unit, hold-up initiating device, door contact, or tamper switch, a condition that the software has determined constitutes and alarm, that indicates an emergency, fire, burglary condition requiring immediate action (Alarm Condition).
5.5 - Automation System
▪A computer system that consists of hardware and software components.
▪These components include the alarm-monitoring software supplied by the automation system developer (Micro Key Solutions), the operating system (Microsoft), the (various) programming languages, required to make the system operational.
5.10 - Batch Clear Alarm - A process or utility that allows the blanket clearing of alarms by type, geographical area, and/or priority (see Alarm Stack Maintenance).
5.16 - Computer Cluster - (High-available or Failover clusters)
▪A group of two or more computers that are connected to form redundant nodes which are used to provide service when system components fail [see (a) UL Installation Requirements, (b) MKS Systems Status, and (c) MKS Cluster].
▪Such high-availability or failover clusters are designed to use redundancy of cluster components to eliminate single points of failure.
5.17 - Cold System - A system whose sole purpose is to be available in the even that the main system has experienced a catastrophic failure. The system is only turned on to update the software, the software configuration, and the database, and then is turned off until needed. Manual intervention is needed to bring the system online and to make it the active monitoring system.
▪See [** Optional PC/Server] identified in UL Installation Requirements and its Micro Key UL Configuration Diagram
5.21 - Fault Tolerant Computer System
▪A computer system containing multiple power supplies, disks, processors, and controllers, each backing-up and checking on the processes of the others [see (a) UL Installation Requirements, (b) MKS Systems Status, and (c) MKS Cluster].
▪In the event of a component failure, the other modules take over the job performed by the failed component without affecting the operation of the computer.
▪In addition to the duplicate hardware, a fault-tolerant system includes software components consisting of the operating system, programming languages, the alarm-monitoring software supplied by the automation system software developer required to make the system operational.
▪See 5.25 and 5.43 for the definitions of a Hot back-up and a redundant system.
▪A fault-tolerant computer system as defined above is considered to be redundant.
5.25 - Hot Back-up - A continuously energized computer system that is a back-up to the primary system computer and disk drive [see (a) UL Installation Requirements, (b) MKS Systems Status, and (c) MKS Cluster].
5.34 - National Institute of Standards and Technology (NIST) - An agency of the U.S. Department of Commerce that works with industry to develop and apply technology, measurements, and standards as needed by industry or government programs such as encryption security.
5.41 - Receiving Software
▪Software residing on a computer or network server that monitors the status of protected premises and stores status changes in memory (see SPA --Signal Processing Application).
▪The receiving software connects to the automation system and transmits signals received from alarm systems to the automation system (see Alarm Stack).
5.43 - Redundant Computer System (see MKS System Status Application and MKS Cluster).
▪Two or more computer systems maintained at a central-station, either of which can quickly be connected and operational for processing signals in the event that the other computer fails to operate.
▪A fault tolerant computer system is considered to be redundant.
5.47 - Runaway System
▪Any alarm system that transmits a greater number of the same type of signals from a particular device, point of protection, zone (or in the absence of the availability of such detail) the overall system, then the automation system is preprogrammed to received within a preprogrammed period of time (see On Runaway Alarm in SPA Setup - System tab).
▪The number of signals and the time from which define a runaway system are agreed upon by the central-station and the automation system software provider .
▪An automation system programmed with the runaway system criteria provided by the central-station meets the requirement of 11.1.9.
➢Also see:
a)Runaway Count - This is a SPA specific setting and matches the associated Count value established in the System tab in the Setup Form within SPA (see the On Runaway Alarm section in that System tab chapter for more information).
b)Runaway Min - This is a SPA specific setting and matches the associated Minutes value established in the System tab in the Setup Form within SPA (see the On Runaway Alarm section in that System tab chapter for more information).
iv.Runaway Start field in Panel Info tab
5.53 - Subscriber
▪The user of a premise or item protected by a burglar or fire alarm system.
▪An authorized representative of a user is also considered a Subscriber
➢Within these MKMS Help Files, any Central Station Monitoring Customer is a Subscriber (who may also be referred to as an Account).
5.55 - Supervised Burglar Alarm System - An active alarm system in which operators initiate follow up actions when an anticipated signal, such as an opening and closing, or check-in signal is missed or improperly sent (see Events).
5.59 - Unscheduled Opening - An opening of a burglar-alarm system not made in accordance with an established schedule (see Events).
5.62 - Watchdog Timer - A hardware or software supervisory module which supervises the disk drives, micro-processors, power supply output, and similar components [see (a) UL Installation Requirements, (b) MKS Systems Status (c) MKS Cluster], and Watch Dog Timer].
Functionality Requirements
❑6 Automation Access Security
6.1.1 - Any connection to the system that permits access from a point outside the central-station shall be through a secure, end-to-end connection that utilizes encryption certified by NIST (see 5.34).
▪The configuration of these connections used in central-stations shall comply with Section 17.12, Connections to the Computer System, or the Standard for Central-Station Alarm Services, UL 827.
6.1.2 - The system shall record the following (User Login History Report):
a)User Name
b)The time access was made; and
c)The date access was made
6.1.3 - After 5 unsuccessful Access Attempts within 10 Minutes, the User's Access shall be disabled.
6.1.4 - Maintain Sign in Records - Any External Log In's Time & Date with the Changes, User ID, Data changes, Email and Printouts.
▪These requirements are managed as if the User was internal to the system Audit Reports, Daily Accounts Modified, User Login History Report).
6.1.5 - Confirm Sign-in Right - Record Keeping to confirm User requesting Access has that Authority (User Login History Report).
6.1.6 - User Tracking - Record the addition and termination of Users (see Employee Hired/Terminated).
6.2.1 - Username and Password Rules - Each security sign-on shall consist of the following (see Change Passwords):
a)A Username of at least six (6) characters.
b)A Password which shall consist of a minimum of six alpha-numeric characters with at least one alpha and one numeric character.
6.2.2 - Personal Sign-in Identity - Each individual using the automation system must have a personal sign-on, and when signing in, the system shall create a record including the following (User Login History Report):
a)Time
b)Date
c)Employee ID
6.2.3 - Track User Changes - Any modification made to the database shall be logged with a unique personal identification (Employee ID) belonging to the person performing the modification (see Audit Reports, Daily Accounts Modified, and Email Modified Subscribers Now for more information).
6.2.4 Passwords Expire in 3 Months - Password Expiration Requirements for mandatory password changes (see Change Expiring Password):
▪Check the Passwords Expire? box within the Company Options tab of the User Options Form.
▪Set the frequency that this must occur in the Passwords Expire in xx Days field to a maximum of 90 Days (see Change Passwords).
6.2.5 - The system shall not authorize the user to gain access if the security sign-on is not changed after the prompt.
6.2.6 - The system shall prohibit the following passwords (see Change Passwords):
▪The CheckULPasswordRestrictions option in Company Settings must be set to True ("T") to comply with Section 6.2.6 relating to Password Restrictions in the Third Edition UL® 1981 Standard
a)Repeated passwords, used within the last six changes;
b)Passwords that are a derivative of the user name(s); and
c)Passwords that are simply letters or numbers in order (e.g.: abcd, 1234, etc.).
▪6.2.6 effective April 29, 2016
6.2.7 - Once communication of a session has been idle for a maximum of 15 minutes the session shall be automatically terminated (Inactivity Disconnect).
▪6.2.7 effective April 29, 2016
•6.3 - Sign-on Security Levels
6.3.1 - The Security sign-on shall govern the access level to the automation system.
➢The Employee Groups Form, User Access Rights Form, and the Employee Form's Security tab provide this capability
6.3.2 - The automation system shall have a minimum of five levels (or degrees) of security.
▪The ability to handle or acknowledge signals shall be able to be disabled independently by all individual user levels at any security level may be established (see Denying Access Rights).
▪All of the privileges of each security level are available to the next higher security level (see Employee Groups).
6.3.3 - Minimum Security Level (see Employee Groups):
a)Shall permit processing and acknowledgment of operator actions in response to signals received from alarm systems; and
b)Shall permit printing or electronic copying of alarm system records
6.3.4 - Second Security Level (see Emergency Management Mode):
a)Shall permit temporary, 24 hour maximum, suspension of the automation system's designated activity for specific functions of an alarm system;
b)Shall automatically restore the suspended alarm systems within a predetermined time;
c)Shall be restored upon a change of functions; and
d)Shall permit repeated suspensions of alarm systems.
6.3.5 - Third Security Level shall permit permanent record changes to automation system's alarm system data base such as adding, deleting (see Employee Groups and User Access Rights), suspending accounts longer than 24 hours.
▪See Update Employee Information, and Central Station sub-tab
6.3.6 - Fourth Security Level (see Employee Groups and User Access Rights):
a)Shall provide the ability to:
1)Create and/or change system IDs; and
2)Make changes to time and date
b)The user shall not be able to change the time and/or date of the following status signals:
1)Dispatch information;
2)Arrival information; or
3)Alarm signal information.
6.3.7 - Fifth Security Level (see System Administrator):
a)It is intended to be a level only accessible to the software provider's programmers, or end user IT staff; and
b)Shall provide capability for permanent modification of the alarm monitoring software.
➢The Security & Access Management section and its related Employees, Employee Groups, Add/Delete Users, User Access Rights and Form Names chapters provide the means and methods available to establish the required security levels.
❑7 Automation Multiplicity
7.1.1 - The primary system (reference Third Edition UL® 1981 Standard Section 9 - Equipment) shall be capable of supporting a "hot back-up" redundant system, that shall be capable of being on-line, monitoring signals, within 90 seconds.
▪This may take the form of:
a)Another "hot" computer system [see (a) UL Installation Requirements, (b) MKS Systems Status, and (c) MKS Cluster]; or
b)A fault tolerant system computer system; or
c)a computer cluster.
7.2.1 - If supported by manufacturer, there shall be a watch-dog timer to provide supervision that the automation system(s) are operating as intended.
▪Should one of the automation systems become unable to process signals, an audible and visual signal shall be annunciated (Watch Dog Timer).
▪Exception: A watchdog timer is not required if the automation system meets the following (MKS Cluster):
a)The automation system monitors the operation of all active computers and receivers.
b)The automation system is capable of generating an audible and visual signal within 90 seconds of the occurrence of the fault; or
c)A visual display condition under the failure or switchover condition is obvious to the operator may be used in lieu of both a visual and audible signal.
❑8 Processing Signals from Monitored Systems (Automated Alarm Processing Procedures, Operator Guided Response, Action Plans, plus Signal Processing and related subordinate chapters)
•8.1 - All Signals from fire alarm systems shall be handled in accordance with the National Fire Alarm and Signaling Code, NFPA 72
•8.2 - All Signals from burglar alarm systems shall be handled in accordance with the Standard for Central-Station Alarm Services, UL 827
❑9 Equipment
•9.1 - Computer systems used in an automation system shall comply with the Standard for Information Technology - Safety - Part 1. General Requirements, UL 60950-1 and the Standard for Central-Station Alarm Services, UL 827.
•9.2 - Computer system shall be designated, by the manufacturer with the following minimum specifications (UL Installation Requirements):
a)Designed for continuous use, 24 hours per day, 7 days per week;
b)Be specified by the manufacturer as a "high-availability" system;
c)Have no less than two cooling fans;
d)Have no less than two power supplies, each of which can supply power for the entire system;
e)Have no less than two network connections, each of which can service all the system's needs.
❑10 Reports and Records (also see the list of Reports and Records at the end of this chapter)
•10 - General
10.1.1 - All recorded data shall be recorded on non-volatile memory.
✓Each Alarm Processing step, all Alarm History, Subscriber Data (and associated changes), etc. are stored permanently, until that data is selectively deleted, based on its storage time requirement (see Central Station Reports),
10.1.2 - The system shall be capable of printing change-of-status signals upon demand when given the Account Number (CSID), Date, and Time, as appropriate.
✓The Alarm Activity Report (designed and documented to comply with the Third Edition UL® 1981 Standard) provides many options to selectively Choose the Alarm Signal Activity data that will be included on the report.
10.1.3 - Upon resolution of any incident resulting in an alarm signal being received, the automation system shall record the following information about all accounts which shall include the following items (Alarm Ticket Report), as applicable:
a)The name and address of the Subscriber;
b)The type of alarm (Alarm Condition);
c)The designated response time [UL Response Time (minutes) & UL Classification is identified in the Central Station Data section for the Subscriber];
d)If alarm system has line security whether it is standard or encrypted line security (Panel Connect ID description as entered in the Panels Info tab for the Subscriber);
e)The time the alarm was received by the automation system (information is captured, recorded in the Signal History table, and included in the Alarm Ticket Report automatically);
f)The time the alarm signal was acknowledged (information is captured, recorded in the Signal History table, and included in the Alarm Ticket Report automatically);
g)Alarm Verification (if used) - (information is captured, recorded in the Signal History table, and included in the Alarm Ticket Report automatically);
h)The time the police/fire department was notified (information is captured, recorded in the Signal History table, and included in the Alarm Ticket Report automatically);
i)The identification of the police or fire department personnel that were notified (entered by the operator and then captured, and recorded in the Signal History table, and included in the Alarm Ticket Report automatically);
j)The time the alarm runner No. 1, if any, was dispatched and the investigator's name and employee ID (entered by the operator and then captured, and recorded in the Signal History table, and included in the Alarm Ticket Report automatically);
k)The time the alarm runner No. 2, if any, was dispatched and the investigator's name and employee ID (entered by the operator and then captured, and recorded in the Signal History table, and included in the Alarm Ticket Report automatically);
l)The time the alarm runner No. 1 arrived (if dispatched) - (entered by the operator and then captured, and recorded in the Signal History table, and included in the Alarm Ticket Report automatically);
m)The time the alarm runner No. 2 arrived (if dispatched) - (entered by the operator and then captured, and recorded in the Signal History table, and included in the Alarm Ticket Report automatically);
n)The elapsed time between the receipt of the alarm at the central-station automation system and the arrival of the runner at the protected premises (information is calculated, recorded in the Signal History table, and included in the Alarm Ticket Report automatically);
o)The method used to verify the alarm arrival of the runner such as radio, telephone, or other means (Noted by the operator and then captured, and recorded in the Signal History table, and included in the Alarm Ticket Report automatically);
p)Whether the Central-Station holds keys [Keys Held as entered in the Central Station Data section for the Subscriber];
q)Whether the Keys were used or not used (Noted by the operator and then captured, and recorded in the Signal History table, and included in the Alarm Ticket Report automatically);
r)The time the subscriber(s) was notified (information is captured, recorded in the Signal History table, and included in the Alarm Ticket Report automatically);
s)The name of the notified subscriber (information is captured, recorded in the Signal History table, and included in the Alarm Ticket Report automatically);
t)The alarm resolution (the Resolution Code is entered by the operator and then captured, and recorded in the Signal History table, and included in the Alarm Ticket Report automatically);
u)Identification of the operator who processed the alarm (information is captured, recorded in the Signal History table, and included in the Alarm Ticket Report automatically);
10.1.4 to 10.1.5 are accommodated by the automation system as part of its regular process of managing Openings and Closings (see Events, Open and Close Report, and Still Open or Closed).
10.1.6 - If supported by the manufacturer (Service Tracking System), records of any Inspection, Testing, and Maintenance action (Automating Recurring Service) shall include the following:
a)Nature of Service (Work Order);
b)Specific Equipment inspected, tested, or serviced (Completing the Work);
c)Name of central-station representative performing service (Scheduling, Technician Activity); and
d)Any follow-up or additional action taken on unwanted alarms (Chaining a Work Order, False Alarm Tracking).
10.1.7 - Account Specific Reports (see Service Tracking Reports, Central Station Reports)
•10.2 - System Wide Reports
10.2.1 - The automation system shall be able to output the following standardized statistical reports (UL Statistic Report) both by certified accounts, non-certified accounts and both combined as indicated below:
a)If the central station has multiple locations then the totals must be broken down by each central station location that is responsible for delivering monitoring services.
b)Certificated account activity shall include the statistics as specified in 10.2.(a) - (g).
▪10.2.1 effective April 29, 2016
10.2.2 - The following shall be used in calculating this performance (see UL Statistics Report):
a)As a minimum. the most recent full month in which 100 or more alarm investigations have occurred, shall be used;
b)At a maximum, the alarm investigations that occurred in the most recent six months shall be used;
c)Alarms for which a runner was required but not dispatched or did not arrive shall be included in the calculation;
d)All statistics shall be broken down by certificate type, such as fire alarm systems, central-station burglar alarm systems, proprietary burglar alarm systems, national industrial burglar alarm systems, mercantile burglar alarm systems, or residential burglar alarm systems, and account number;
e)Total number of events, requiring operator action, that occurred in certificated accounts;
f)Operator acknowledgment time shall be listed by longest time, average time, and shortest time; and
g)Runner response elapsed time shall be listed by longest time, average time, and shortest time. Elapsed time shall be determined by using the difference between the time recorded for the receipt of the alarm signal ([See 10.1.3(e)] at the central station, and the time recorded at the central station as a result of a signal given by the runner representing the operating company upon arrival at the entrance of the subscriber's premises. See 10.1.3(i).
▪10.2.2 effective April 29, 2016
10.2.3 - The automation system shall be able to process signals that are able to be displayed by a receiver to which it is connected (see SPA Setup- Receivers tab, Communicator Formats, Processing Alarm Signals).
❑11 Human Interface
•11.1 - General
11.1.1 - Each operator station that displays change-of-status signal shall have an audible or visual means of alerting the operator to the receipt of a change-of-status signal (see Processing Alarm Signals and Verification - Validating the Alarm).
11.1.2 - The following change-of-status signals shall be indicated to the operators
a)Alarm conditions (see Alarm Conditions and CSID Zones);
b)Supervisory conditions (see Events and Other Events);
c)Trouble conditions (see Trouble Signals); or
d)Restoral conditions (see Restoral Information).
11.1.3 - A minimum of one central-station operator or supervisor is logged on at all times (see Processing).
11.1.4 - When only one operator or supervisor is logged on, who then attempts to log out, a message shall inform the operator/supervisor that she/he is the last one logged on (see Completion).
11.1.5 - The time, date, type, and location of all signals received by the central-station and requiring operator action shall be automatically recorded (see Alarm History Look Up and Alarm Activity Report) and displayed (see Processing Alarm Signals) in a form that will expedite prompt operator interpretation in accordance with the following:
a)Routine signals such as disarming and arming (opening and closing) [see Events], and periodic check-in signals complying with the schedule (see Account Testing) shall not be displayed.
b)A status change signal that is acknowledged shall be displayed differently from a status change signal that has not been acknowledged (see Alarm Stack).
c)When an audible signal that alerts the operator to receipt of a change-of-status signal is silenced, it is to be re-energized upon receipt of a subsequent change-of-status signal with higher priority from the same account or a change-of-status signal requiring operator action from another account (see Company tab & Company Settings: items n. o., p., q. and Company Settings - Priority Alarm Notification).
d)There shall be the means provided for an operator to redisplay the status of signals that have been acknowledged and not yet restored to the normal condition (see Non Restored Signals and Docking Options).
e)When the system provides for continuous retention of the signal on visual display until manually acknowledged:
1.Subsequent recorded presentations shall not be inhibited upon failure to acknowledge (SPA, Alarm Stack); and
2.The visual display shall indicate that additional signals are pending (see Docking Options-Pending Signals)
f)When only a single display is provided, fire alarm signals shall be given priority status (Setting Alarm Condition Priorities) on the common visual display (see Alarm Conditions, Company Settings - Priority Alarm Notification)
g)Multiple Function systems shall be configured according to the following functions in descending order of priority (Setting Alarm Condition Priority Levels, UL® Alarm Condition - Priority Ranking ):
1) Fire alarm;
2) Emergency call system; (mass notification / E911 / reverse 911 / fire system);
3) Hold-up or panic alarm;
4) Medical including carbon monoxide;
5) Industrial supervision if a danger can result;
6) Burglar alarm (with line security);
7) Burglar alarm (without line security);
ÙÙÙÙÙÙÙÙ
Above the arrows are required (priorities 2,3,4 may share the same priority number)
8) Supervisory signal
9) Trouble signal;
10) Other.
▪Items 2, 3, and 4 are not prohibited from having equal priority.
▪See Alarm Priority Cutoff.
h)The signal information content shall be recorded for both alarm and restoration to normal conditions (see Alarm History Look Up and Alarm Activity Report).
11.1.6 - When the operator is working from a menu other than the alarm processing menu, and a change-of-status signal requiring operator action occurs, the automation system shall:
a)Generate an audible and visual indication of the signal (Processing); or
b)Generate an audible signal that continues until the operator resumes alarm processing (Processing Alarms, Alarm Stack, Processing).
11.1.9 - The automation system shall be able to automatically identify an alarm system as a runaway system (see 5.47 - Runaway System) when the number of signals from that system exceeds the pre-programmed number wit the pre-programmed time frame; the following shall occur (see Special Panel Zones, Mandatory Condition Codes & Panel Zones, On Runaway Alarm in SPA Setup - System tab):
a)It shall immediately and automatically display a message on the operator terminal; and
b)The message shall indicate"runaway" system and identify the details of the alarm system such as type of signal, account number, location, contact person, and similar information.
▪The automation system supplier shall ensure that the "runaway" counter minimum threshold is more than the "swinger-shut-down" maximum of ANSI/SIA CP-01-2010 count (standard six trips).
▪11.1.9 effective April 29, 2016
•11.2 - Automation software components
11.2.1 to 11.2 (a-c) - (See 11 - Human Interface, 11.1 General 11.1.1 - 11.1.9 for the compliance Links)
11.2.3 - Upon receiving a signal from a receiver, the system shall time and date stamp with the record and shall:
a)Prioritize the alarms in the order required (see 11.5.,g) and (Setting Alarm Condition Priority Levels, UL Alarm Condition - Priority Ranking);
b)Deliver the new signal to the next available operator in the alarm queue (Alarm Stack, Processing Alarm Signals);
c)Move certificated system alarms to the top of each respective priority queue (Alarm Stack, UL Systems Prioritized in Alarm Stack); and
d)Cause an alert when events at given priorities exceed specific wait times (see 11.2.5)
11.2.4 - If supported by manufacturer, batch alarm clear shall be done by an authorized individual with a third for fourth sign-on security level.
▪The batch alarms shall have an option to exclude fire alarms and certificated systems (Alarm Stack Maintenance, Advanced).
11.2.5 - An alarm pending in the automation alarm queue that goes unprocessed in excess of 90 seconds shall generate an alarm at the central-station signifying there is an alarm pending for handling at the remote site that has not been claimed in over 90 seconds (Overdue Signals - Docking Options).
.
❑12 - System Connections from Outside the Central-Station
•12.1 - The central-station software shall provide for security verification for remote user access that is at least equal to security standards for personnel having access internal to the system location as found in Section 6, Automation Access Security.
▪12.1 effective April 29, 2016
•12.2 - If supported by the manufacturer, when access to the system is not over a secure access point and there is no means of verifying the user, there shall be no access (no unsecured access is permitted).
▪12.2 effective April 29, 2016
•12.3 - If supported by the manufacturer, security measures shall be implemented to limit data access to information needed based on the user type or device type. Limitations shall be based on:
a)Geography;
b)Customer type;
c)Business type;
d)Service type.
▪12.3 effective April 29, 2016
•12.4 - If supported by the manufacturer, service technicians shall utilize field equipment that is registered within the monitoring station's database to view data and/or conduct system testing functions including:
a)On test;
b)Off test; and
c)Test results.
▪12.4 effective April 29, 2016
•12.5 - If supported by the manufacturer, forms of communication between the technicians and the system include but are not limited to:
a)Voice automation;
b)Dual tone multi-frequency signaling (DTMF); or
c)Smart device.
▪12.5 effective April 29, 2016
•12.6 - If supported by the manufacturer, all employees capable of changing data shall provide security sign-on codes as found in Section 6, Automation Security.
▪12.6 effective April 29, 2016
•12.7 - The automation system shall be capable of immediately sending electronic notifications to the designated end user any time a data change is made to a subscriber account (Email Modified Subscribers Now).
▪12.7 effective April 29, 2016
•12.8 - Forms of connectivity between the system and the subscriber include but are not limited to:
a)Voice automation;
b)Text messaging;
c)Electronic email;
d)Smart devices; or
e)Internet.
▪12.8 effective April 29, 2016
•12.9 - The ability to change data shall not include the capability to change a user account.
▪12.9 effective April 29, 2016
•12.10 - Violations of rules stated in the Section shall create an alarm condition for response by the central-station (not permitted).
▪12.10 effective April 29, 2016
❑13 - Hardware Receiver Requirements
•13.1 - The automation software developer shall provide an information screen that will list all compatible receivers (SPA Setup- Receivers tab, Communicator Formats).
▪13.1 effective April 29, 2016
Performance
❑14 System Performance
•14.1 - General
14.1.1 - Except as otherwise indicated, the performance of the automation system shall be investigated by subjecting a representative sample in commercial form to the tests described in Sections 14 through 16.
▪The chart in Appendix B (of the Third Edition UL® 1981 Standard) may be used as an example for documenting the performance check).
•14.2 - Performance Monitoring (MKS System Monitor)
14.2.1 - The amount of unused capacity of the central processing unit (CPU) and data storage systems for each computer and the bandwidth of networks shall be stored as a report. If the utilization exceeds 80% an audible and visual notice shall be annunciated in the operating room and the technical support staff shall be notified. The technical support staff shall retain a record of notice.
14.2.2 -The report shall include the following:
a)The percentage of utilization of the central processing unit (CPU) shall be recorded in at least 20% increments, starting at less than 20% and going up.
b)The percentage utilization of the disk arrays shall be recorded in at least 20% increments, starting at less than 20% and going up. When applicable to both:
1)Any constraints to the database resulting from its configuration shall be recorded.
2)Any constraints to the data storage system shall be recorded.
c)The percentage of utilization of the bandwidth for any local are networks or wide area networks that are used in conjunction with the automation system shall be recorded in at least 20% increments, starting at less than 20% and going up. If the utilization of any of these exceeds 80% averaged over 15 minutes an audible and visual notice shall be annunciated in the operating room.
▪14.2.2 effective April 29, 2016
•14.3 - Signal processing throughput
14.3.1 - An automation system shall make signals, requiring operator action (SPA), available to the operator within ten (10) seconds of the receiver making it available to the automation system (Alarm Stack).
❑15 - Normal Operation Test
•15.1 - An automation system shall be capable of operating for all conditions of its intended performance as indicated in the user's instruction manual (Help Files) when used in conjunction with the equipment indicated by the installation wiring diagram (UL Installation Requirements) and information supplied with it.
•15.2 - To determine compliance with 15.1, the compatible receiving and transmitting equipment is to be connected to an automation system as specified by the installation wiring diagram (UL Installation Requirements) to form a typical combination.
▪The system is then to be operated for each condition of its intended use as started in the user's manual (Help Files).
▪An example of a worksheet for recording data is shown on the Automation System Check Sheet found in Appendix B (of the Third Edition UL® 1981 Standard).
❑16 - Operation Test - Degraded Mode
•16.1 - Upon failure of the automation system - whether redundant or non-redundant - the required functions of the receivers connected to the automation system which may be suppressed shall:
a)Revert to their normal operation;
b)Automatically print all change-of-status signals and generate an audible signal under the degraded mode of operation; and
c)Not cause a loss of signal when the system enters degraded mode.
•16.2 - When an automation system is operating in a degraded mode, change-of-status signals shall be processed manually.
•16.3 - Whether the automation system is a non-redundant or redundant system, all of the following records shall be maintained and readily available at the central-station (Sub Info (F2), Subscriber Information Forms).
▪Exception: The maintenance of records requirements shall be superseded by requirements of the Standard for Central-Station Alarm Services, UL 8237, Alarm Monitoring Systems.
➢Also see 5.17 - Cold System and [** Optional PC/Server] identified in UL Installation Requirements and its Micro Key UL Configuration Diagram
a)Dispatch Instructions (CSID Zones);
b)Arming and disarming, (opening and closing) schedules (Events);
c)Pass card data (Sub Info (F2)) ;
d)Holiday observed schedules (Events, Holidays), and the time and date that the data file was created;
e)Meet the requirements specified in the Records sections (fire alarm, and burglar alarm) in the Standard for Central-Station Alarm Services, UL 827, as appropriate (Subscriber Information Forms);
f)A means to permanently record the date and time the action was taken to respond to change-of-status events (Alarm History Lookup); and
g)A means to transfer the data from Manually-generated activities into the automation system's permanent record when the automation system is back in normal operation, shall be provided (Manual Signal Entry).
•16.4 - An audible trouble signal or visual display that is obvious to the operator shall activate within 90 seconds of an occurrence of the following malfunctions (MKS Cluster, MKS System Status Application)
a)The automation system does not execute its program cycle;
b)A power-supply output upon which the operation of the automation system relies (such as a micro-processor, memory, disk drive, or similar equipment) ceases to operate; or
c)Disk rotation ceases, or fails to start when required, in an automation system that incorporates permanent memory-storage devices having rotating elements.
▪Exception: When each and every receiver compatible with the automation system provides the audible indication within 90 seconds for the conditions (a) - (c), then it is not required that the automation system have a separate watchdog timer (see Section 13, Hardware Receiver Requirements, and 17.8)
•16.5 - The alarm-monitoring capabilities of the automation system shall not be affected when it executes or fails to execute any supplementary program.
•16.6 - Electrical Supervision
16.6.1 - If supported by the manufacturer, the installation of the automation system components shall provide the electrical supervision described in 17.14.2, Electrical Supervision, of the Standard for Central-Station Alarm Services, UL 827.
Instructions
❑17 - General
•17.1 - A copy of the operating and installation instructions (Help Files) shall be provided with the automation system submitted for investigation and shall be used as a guide in the examination and test of the system.
•17.2 - The operation instructions shall include concise descriptions of the following:
a)Operation (Central Station Monitoring);
b)Testing (Testing Procedure for Failover);
c)Maintenance procedures (Failover Testing Procedure); and
d)Recommended testing frequency (Monthly).
▪17.2 effective April 29, 2016
•17.3 - The installation instructions shall have a section or sections which specifically describe each of the following equipment requirements for the automation system:
a)The system configuration (UL Installation Reference, UL 1981 Third Edition Standard - Overview (this chapter), UL Installation Requirements, UL Settings, Signal Processing & Reporting Procedures)
b)A listing of which hardware or software systems are compatible (UL Installation Reference, UL Installation Requirements);
c)All elements of the automation system (UL Installation Reference, UL Installation Requirements); and
d)A description of how to protect data when external connections are available (Security & Access Management).
•17.4 - The installation instructions shall include minimum system specifications regarding (UL Installation Reference):
a)Operating system; and
b)Revision level.
•17.6 - The installation instructions shall include a list of components for the minimum system configuration for:
a)Redundant systems (UL Installation Requirements); and
b)Non-redundant systems
•17.7 - The list of components shall include (UL Installation Reference, UL Installation Requirements, Micro Key UL Configuration Diagram):
a)Video display terminals;
b)Printers;
c)Computers
d)Watch dog timers (Watch Dog Timer, MKS System Monitor, MKS Cluster); and
e)Instructions on how to display the software version (revision) [About (MKMSCS)].
•17.8 - The installation instructions shall include a complete list of compatible receivers and the output formations that are supported by the automation system (SPA Setup- Receivers tab, Communicator Formats).
❑Reports and Records
•Sample of the Third Edition UL® 1981 Standard related Central Station Reports
✓The following Reports for Certificated Accounts are stored for a minimum period of One Year and may be reproduced whenever required during that time period:
a)Alarm Tickets must be stored (and reproduced on demand) for each Alarm Event, including the UL® Grade information for each applicable Subscriber's Alarm System.
i.See the UL Definitions chapter and UL Glossary/MKS Terminology chapters for definitions relating to the Third Edition UL® 1981 Standard.
ii.See the UL Signal Processing Procedures chapter for detailed information.
b)Active/Passive Report which lists the total number of Active System (Accounts that are being Actively monitored) - offering Detailed and Summary versions of this data.
c)Alarm Activity Report which provides many options to selectively Choose the Alarm Signal Activity data that, among others, will list Fire Alarm, Panic/Hold Up Alarm and Burglar Alarm Condition Codes.
d)Dealer Breakdown Report which provides a listing of each Dealer, their Accounts, related reporting and signal data, and summary information about each Dealer.
e)Open/Close Reports which lists each Opening and Closing Event records that match the selected Report Options.
f)Employee Hired/Terminated - The Employee Hired/Terminated report (designed and documented to comply with the Third Edition UL® 1981 Standard) provides a list of the Company's Employees is displayed in a functioning Grid dialog with an Employee Trace Form Title. It provides a list of the Employees - retrieved based on their Hire, Termination, or original Entry Date - that is displayed in Grid format and so may then be viewed, sorted, filtered, reconfigured, printed, emailed, and/or exported.
g)Signals While On Test will list those signals received from a Subscriber (Account), and/or a Subscriber Panel (CSID) that occurred while that Account or CSID was On Test.
h)Accounts Without Email - The Accounts Without Email Report (designed and documented to comply with the Third Edition UL® 1981 Standard) will list those Subscribers (Accounts) without an Email address in the Subscribers tab of the Subscribers Form: Edit View and may be produced for All Accounts, or for UL® Accounts Only.
i)UL Statistics - The UL Statistics Report was specifically designed to comply with the System Wide Reports Section 10.2.2 (a) - (g) of the Third Edition UL® 1981 Standard.
j)User Login History Report - The Users Login History Report (designed and documented to comply with the Third Edition UL® 1981 Standard) will list those Employees who have attempted to, or successfully Logged Into the MKMS database.